SECURITY COMPLIANCE AND READINESS ASSESSMENT
Prove Organizational Compliance with Regulatory Standards
As organizations win bigger contracts and work in new countries, compliance with regional privacy laws and industry regulations can become a pain point. Further, these laws are likely to become more comprehensive over time. We help organizations meet regulatory requirements, including PCI DSS, NIST / CMMC, HIPAA, ISO 27001, and GDPR.These services are designed to help organizations:
Ready to talk about Cybersecurity Compliance Solutions?
Call a Connection cybersecurity expert today:Keep Up with Compliance and Certifications
Our assessments guide you through the complex regulatory landscape, ensuring continuous compliance and safeguarding of your organization. Connection’s Managed Services can also help organizations stay compliant with continuous support to maintain ongoing compliance as regulations and threats evolve.Connection assists with compliance and certification for the following areas:
- SOC 1 & 2
- FISMA / FedRAMP
- GDPR
- CCPA
- FFIEC, GLBA, NCUA
- HITRUST
- HIPAA
- PCI - DSS
- NIST Standards such as 800‑53, -171, CSF
- CMMC
- ISO 27001

Security Compliance and Readiness Assessment
What Is It?
- A thorough assessment of gap and compliancy aligned to major regulatory requirements
- Assessment suite tailored to your specific systems, configurations, and policy needs
- Detailed gap analysis and actionable recommendations
- Expert guidance from certified security professionals
Deliverables
- Detailed Risk Assessment Report with Prioritized Remediation Roadmaps
- Compliance Gap Analysis
- Raw Scan Results with Top25 Mitigation Report
- Attestation of Compliance
- Certificate of Compliance
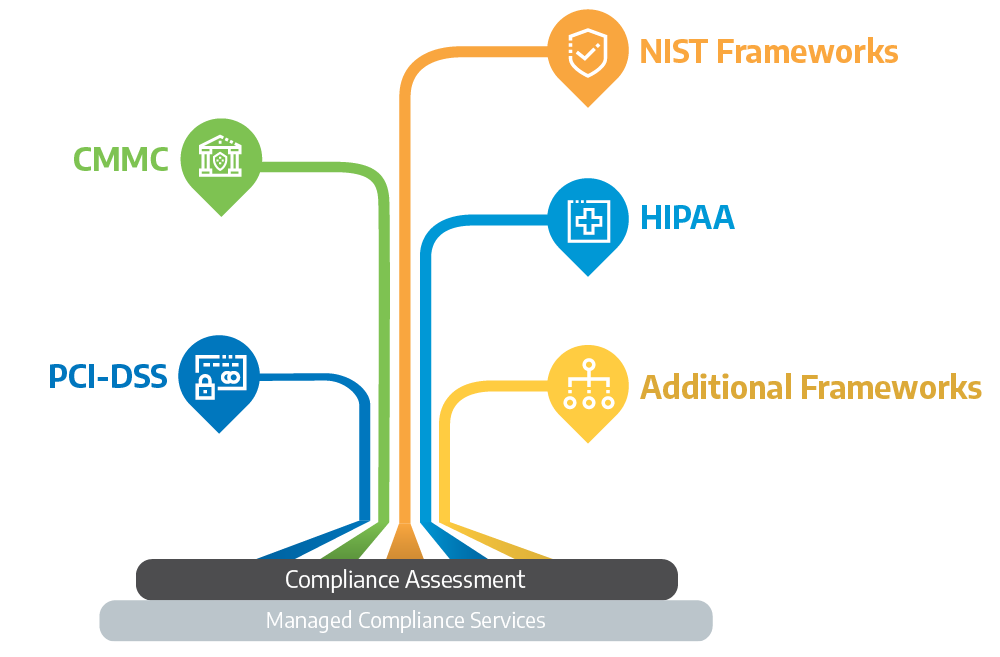
CMMC
Customers who work with the Department of Defense or are in the DoD supply chain; CMMC has a large impact across many organizationsIndustries: Defense Contractors, Manufacturing, IT
PCI-DSS
Organizations who process, store, or transmit credit card dataIndustries: Retail, E-commerce, Finance, Service Providers
NIST Frameworks
Customers who choose to enhance their overall security posture; this is not a regulation or mandated for most organizationsIndustries: IT, Healthcare, Manufacturing, Government
HIPAA
Privacy and security rules that protect the privacy and security of individually identifiable health informationIndustries: Healthcare, Pharma, Health Insurance, Telehealth
Additional Frameworks
Depending on the client’s compliance or regulatory requirements, there may be a need for various Compliance Services. We can assist with many of the auditable frameworks, e.g. ISO, SOC, GDPR, NIS2, DORA, etc.Industries: Applicable to all industries
Security Compliance and Assessment Flyers

Cybersecurity Specialists with Decades of Field Experience
Connection’s cybersecurity specialists have spent years protecting organizations’ data availability and privacy across a range of industries. Each specialist is equipped with the skills and certifications to make each project a success. Connection’s cybersecurity specialists work as trusted advisors with our clients, creating custom solutions to meet your organization’s specific needs.Our industry security certifications include PCI DSS QSA, PCI DSS, PCIP, CMMC RP, CISSP, ISSAP, CCISO, Ethical Hacker, Offsec Wireless Pro, ISO Auditor, SANS, and CSIE.

Ready to talk about Cybersecurity Compliance Solutions?
Call a Connection expert today.
Let’s Connect!
Share your email and a Connection Cybersecurity Expert will reach out to you during our business hours.Connection Community
TechSperience Episode 144: Future...
In this episode, the Connection Security Center of Excellence team looks beyond today’s headlines to uncover the threats most people... Read More
How St. John’s Health and Connection Are...
In the heart of Jackson Hole, Wyoming, St. John’s Health stands as a beacon of care for both its local... Read More
Securing the Future: Key Insights on...
We recently hosted a webinar with Jamal Khan, Chief Growth and Innovation Officer at Connection and Head of the CNXN... Read More
TechSperience Episode 140: Signals of...
In this episode, the Connection Security Center of Excellence Team takes us on a journey—both literal and technical—sharing insights gained... Read More
Data Security and Compliance: Strengthening...
Data security is a critical priority for everyone, especially those who manage sensitive information across a variety of workstreams within... Read More